Cyber Liability Insurance: Data Breach & Cyber Risk Coverage
Businesses across the country need special coverage to protect their networks against data breaches and other virtual threats.

Paul Martin is the Director of Education and Development for Myron Steves, one of the largest, most respected insurance wholesalers in the southern U.S.

Businesses in the US average only 42.53% in preparedness to protect themselves against data breaches and other cyber threats. Since cyber risks are always evolving, it’s important to ensure that your business gets equipped with the right coverage to protect its operations, revenue, and more.
The best way to achieve this is to work with an experienced independent insurance agent. They’ll be with you every step of the way while selecting the right policy for your business and get you set up with cyber liability coverage that considers all your business’s specific risk areas.
What Is Cyber Liability Insurance?
No matter where you’re based, cyber liability insurance is essentially a contract between a business or individual and an insurance company in which the insurer agrees to cover losses from liabilities and other costs related to various cyberattacks. Cyber liability insurance has begun to be offered with standard business insurance policies due to the growing importance and relevance of this coverage.
Though you may not think your business is extremely technical, with just an internet connection, you’re vulnerable to attacks by cybercriminals. Many business owners have unfortunately had to learn the hard way how crucial having coverage really is. It’s best to be proactive about protecting your business, which means getting set up with a cyber liability policy ASAP.
What Does Cyber Liability Insurance Cover?
Cyber liability insurance protects your business against paying out of pocket for costs related to data breaches or other cyberattacks. Costs can stem from the following:
- Lost income
- Notifying affected parties of the data breach
- Recovering compromised data
- Repairing computer systems
- Bank fees for having to cancel stolen credit cards
Cyber liability coverage varies greatly depending on which insurer you get coverage from since these policies aren’t standard across the board. This type of coverage is relatively new, and insurers have started offering cyber liability insurance within the last couple of decades.
Cyber liability insurance protects businesses that store sensitive information or data electronically, carry out any kind of transactions through the use of the internet, and in many other scenarios involving computers. Though your policy may vary slightly, a handful of core coverages is offered by many cyber liability insurance policies. There is also a variety of coverage limits and deductible amounts, as well.
Who Needs Cyber Liability Insurance?
Cyber liability insurance policies are designed to protect your business against lawsuits stemming from cybercrimes, including breaches of confidentiality with customer information, loss of data, electronic theft, loss of income due to temporary suspension of business operations, and other related losses.
Whether your business needs this type of coverage depends on what your business does and what types of data you store electronically. Do you keep medical records, personal information, credit card numbers, or any other data that could damage your customers personally or financially if it got into the wrong hands? If so, you need cyber liability coverage.
Cyber liability insurance may provide several different types of coverage, such as the following:
- Loss of income because of suspended or limited operations
- Loss of income because of a damaged reputation
- Reparations to customers or third-party vendors who suffered a financial loss due to a breach at your company
- Reparations to customers who suffered emotional distress due to a breach at your company
- The cost of hiring expert programmers to fix the problem by patching up company security holes
- The cost of credit monitoring programs for customers who had personal or financial data stolen
Because cyber liability insurance policies aren't standard, not everything listed above will be included in all policies. There may be differences in the coverages you see in different cyber liability insurance policies depending on the insurance carrier.
What’s Not Covered by Cyber Liability Insurance?
Make sure to carefully review your cyber liability insurance policy, preferably with an independent insurance agent, to see which exclusions apply to you. Since cyber liability insurance is so customizable, two policies may not have exactly the same list of exclusions. However, many cyber liability policies don’t cover the following:
- Bodily injury or property damage claims: Cyber liability insurance won’t protect against claims of bodily injury or property damage. That’s where a general liability insurance policy comes in.
- Loss of property: Losing a piece of property, like a phone or computer, is generally covered by commercial property insurance, not a cyber liability policy.
- Criminal activity: Typically, a cyber liability policy won’t insure against fraud, robbery, employee theft, or other crimes. Commercial crime insurance offers this coverage separately.
- Social engineering: Cybercriminals sometimes target their victims through social engineering or tricking people into transferring company funds to their accounts. Not all cyber liability policies cover social engineering. This additional coverage may come with a smaller coverage limit, or it might be an optional add-on.
Often when you purchase a cyber liability policy, you agree to maintain appropriate security measures in order to prevent a cyber incident from happening in the first place. If you fail to maintain these security measures, future claims might get denied.
If an employee accidentally clicks on a phony link that causes malware to corrupt the company’s computer systems, the insurance carrier could deny coverage for failure to use preventive measures if the company didn’t have anti-malware software. Your independent insurance agent can review your company's cyber liability policy with you to see if this clause is listed.
How Much Does Cyber Liability Insurance Cost?
Just like any other type of insurance, the cost of your policy will depend on a number of different factors, including the size of your business and its annual gross revenue. However, the smaller and less risky your business is to insure, the lower the cost your premium will be. This basic formula is pretty standard across all types of insurance coverages out there.
Smaller companies with relatively basic computer operations might pay less than $1,000 annually, while large tech giants with all kinds of security needs might pay closer to $10,000 per year or even more. However, a recent report from AdvisorSmith Solution Inc. found that cyber liability insurance costs an average of $1,500 annually for a policy with a limit of $1 million and a $10,000 deductible. Your independent insurance agent can give you more specific pricing information for cyber liability policies that work for you.
The Best Cyber Liability Insurance Companies
Cyber liability insurance is available from many different insurance companies, and the best way to find the right carrier for you is through working with an independent insurance agent.
While many insurance companies could create a cyber liability insurance policy for you, finding coverage could also depend on the area you live in.
The best insurance companies for cyber liability insurance
| Top Cyber Liability Insurance Companies | Star Rating |
| Travelers |

|
| Liberty Mutual |

|
| Hiscox |

|
| AIG |

|
One cyber liability insurance company outshines its competitors
- Best overall cyber liability insurance company: Travelers Insurance
Travelers Insurance
Travelers insurance is rated “A++” by AM Best and has been in the insurance industry for nearly 170 years.
With a high volume of customer satisfaction, Travelers provides trustworthy, reliable coverage for businesses of all kinds that are in need of critical cyber liability protection.
Liberty Mutual
Liberty Mutual is an excellent carrier for adapting cyber liability coverage to small business needs. Cyber liability coverage comes as part of a general liability policy or a business owner's policy. Data security endorsements are also available to boost your coverage. Coverage limits of up to $1 million are available. Deductibles range from $2,500 to $10,000 per incident.
Hiscox
Hiscox is a highly-rated insurance company with tons of experience writing cyber liability insurance. For more than 20 years, Hiscox's coverage has been protecting businesses from data breaches and more, and the carrier handles at least 1,000 claims each year. The carrier's primary cyber liability insurance policy is designed for small businesses that generate $1 billion or less in annual revenue. Coverage is available in limits of up to $10 million. The carrier offers both first-party and third-party coverage.
AIG
AIG recently won the 2018 award for Cyber Risk Innovation of the Year. The carrier is also highly rated and owns 22% of the cyber liability market — overall the highest share of any insurance company. AIG provides highly customizable coverage that comes with limits of up to $100 million. The carrier provides not only stand-alone policies, but also the option to pair cyber liability protection with an existing general liability insurance policy. The carrier also offers both first-party and third-party coverage.
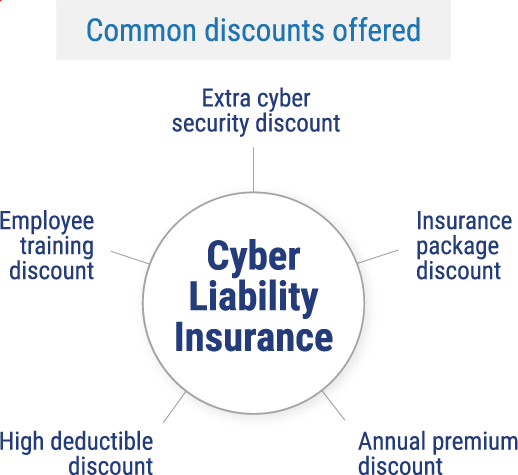
Finding Discounts and Savings on Cyber Liability Insurance
Though the cost of cyber liability insurance can vary greatly and certain policies are more expensive than others, many insurance companies offer a handful of competitive discounts and other ways to save money on coverage. An independent insurance agent is experienced in finding money-saving hacks for cyber liability insurance customers.
Here are a few examples of common discounts offered on cyber liability insurance:
How Much Cyber Liability Coverage Do I Need?
To answer this question, you'll have to analyze your unique business and its operations and risk levels. An independent insurance agent can help you evaluate the amount of risk your company faces for incidents like data breaches. From there, the two of you can work together to figure out an appropriate amount of coverage for your business's needs.
Frequently Asked Questions about Cyber Liability Insurance
Errors & omissions insurance (E&O), also called professional liability insurance, may protect your business against the legal fees associated with a lawsuit after a data breach, but it's not the same as cyber liability insurance. Cyber liability policies are designed to reimburse a company after a cyberattack occurs. Reimbursements can include legal costs, but can also include things like government fines, penalties from credit card companies, costs of hiring professional help, restoration of your data, and more. Those costs are not included in professional liability or E&O coverage.
Frivolous lawsuits supply only weak evidence against your business. These cases are also referred to as “meritless lawsuits” and are often an attempt to get the business owner to hand over a quick settlement payment in a panic. Fortunately, cyber liability insurance covers even legal costs stemming from frivolous lawsuits.
While there are many similarities between cyber liability coverage and data breach insurance, there are some key differences. Data breach insurance is designed to help companies recover from data breaches if customer or other third-party private information gets exposed, stolen, or lost.
Data breach insurance covers these costs:
- PR firm fees
- Credit monitoring service fees for victims of the breach
- Customer or other third-party notification fees
Cyber liability insurance is often bought by large businesses and coverage helps these companies recover after cyberattacks, data breaches, and related incidents.
Cyber liability insurance covers these costs:
- Loss of income because of suspended or limited operations
- Loss of income because of a damaged reputation
- Reparations to customers or third-party vendors who suffered a financial loss due to a breach at your company
- Reparations to customers who suffered emotional distress due to a breach at your company
- The cost of hiring expert programmers to fix the problem by patching up company security holes
- The cost of credit monitoring programs for customers who had personal or financial data stolen
First-party cyber liability insurance helps business owners deal with breaches to their own company, while third-party cyber liability insurance helps protect a business if a breach affects the insured business’s clients. So, first-party coverage can reimburse for incidents that impact the company's network and systems, while third-party coverage can reimburse for incidents that impact customer or client networks and systems.
The four main components of a cyber liability policy are:
- Network security: Covers a business after a data breach, cyberattack, or other related incidents.
- Network interruption: Covers a business for lost revenue, etc., if the network must temporarily shut down after a data breach or other related incident.
- Media liability: Covers a business for acts of intellectual property infringement (not including patent infringement) stemming from its advertising, including advertisements on social media, online, or in print.
- Errors & Omissions: Covers a business for costs related to not correctly or completely fulfilling contracted work for customers, clients, etc., because of a data breach or cyberattack.
Any business that uses computer systems or networks and the internet for its operations needs cyber liability insurance. This ranges from online-based businesses to longstanding small companies that only use the internet to check email. If any private or sensitive data or information can be accessed on a company computer, it’s essential to have this coverage.
If a breach occurs and your business lacks the right cyber liability coverage, you will have to pay for the resulting losses out of pocket. In one recent year, the average cost of a data breach for a company in the US was $8.19 million. Of course, this cost could be a lot less for a smaller company that doesn’t generate much business, but it’s really not worth taking the risk. Any business with important data to protect needs cyber liability insurance.
Standard business liability insurance and property liability insurance coverage are specifically designed to exclude cyber risks. That’s why cyber liability insurance has become a stand-alone product and is so prevalent and frequently recommended by independent insurance agents today.
Since cyber liability policies aren’t standard, you’ll want the help of an independent insurance agent. Together, the two of you will assemble a package of coverages to protect yourself and your business against cyber risks that are unique to you. Cyber liability insurance is designed to keep your business afloat following a huge disaster like a data breach or other cyberattack.
It’s a good idea to be familiar with exactly what your cyber liability insurance policy covers before any incidents ever occur. When a data breach or other event happens that you might have coverage for under your cyber liability policy, you can get in touch with your independent insurance agent or your insurance company directly to file a claim. If the incident is covered, you’ll receive reimbursement according to the terms and limitations in your policy
The Benefits of an Independent Insurance Agent for Cyber Liability & Data Breach Insurance Questions
Independent insurance agents are like the ultimate database of insurance quotes. You tell them what you’re looking for, and they bring in the results. And since they aren’t tied down to one carrier, they’re free to shop around and bring multiple policy options to the table.
https://www.iii.org/article/cyber-liability-risks
https://www.nerdsonsite.com/blog/cyber-attacks-on-small-businesses-how-common-are-they/#:~:text=Only%201%20in%207%20small,%2C%20tools%2C%20plans%20%26%20training.
https://www.embroker.com/blog/cyber-insurance-cost/
https://www.sig.us/what-is-the-difference-between-cyber-liability-and-eo-insurance/
